TECHNICAL SURVEILLANCE COUNTER MEASURES / BUG SWEEPS
OPS CIS is the foremost private investigation company in Phoenix, offering Technical Surveillance Counter Measures (“TSCM”) also known as bug sweep services.
OPS CIS utilizes cutting-edge and industry-leading, counter surveillance detection equipment and bug sweep services in Phoenix to protect clients' privacy and sensitive data. Our team of private investigators can assist in various counter surveillance investigations including:
What is TSCM?
Technical Surveillance Countermeasures (TSCM) refers to services employed to detect the presence of eavesdropping devices used to intercept sensitive, classified, or private information. TSCM is commonly referred to as a “bug sweep.” Bug sweeps utilize specialized equipment engineered to identify a variety of electronic transmitters, mostly common through radio frequencies.
RF Fundamentals
Radio Frequencies (RF) are electromagnetic waves that are propagated through space and are the basis for many different communication systems. Radio waves are identified by their frequency, with a useful communications range between 10 kHz and 100 GHz.
Common RF Signals
Arizona Crimes
TSCM Uses
Our counter surveillance detection services in Phoenix can help prevent loss and or interception of confidential communications
including:
TSCM Limitations
Our counter surveillance detection service in Phoenix is only a small part of a comprehensive data protection strategy. It is not fool-proof and with ever changing technologies TSCM investigators are always needing to adapt. TSCM is part of a “layered” approach to your personal or business security envelope. A bug sweep is only as good as the steps taken afterward to remain diligent about people and items in your spaces.
Types of Bugging / Wiretapping
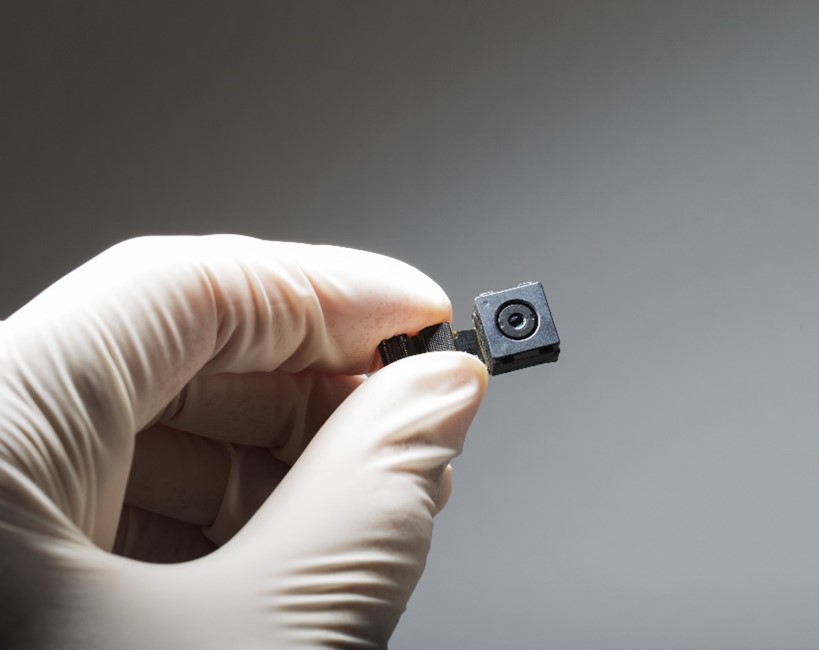

In today's ever-changing digital world, there are numerous security threats to individuals’ and businesses' privacy and confidentiality. From spyware to hidden cameras to audio listening devices, it is easier than ever for strangers to obtain private and personal information about you and your company. The erosion of personal privacy is an increasing and very real threat with the ease of obtaining cheap surveillance goods from the internet. Even worse, there are not enough knowledgeable counter surveillance investigators who can accurately investigate and determine if a person is under electronic surveillance. Many companies use antiquated and substandard counter surveillance detection. Phoenix, like the rest of the world, has sophisticated white-collar criminals who want your data, and that leaves you vulnerable.
OPS CIS offers world class counter surveillance and bug sweeping services in Phoenix and beyond. How can we help?
OPS Consulting and Investigative Services LLC
Live answering 24 hours a day!!
HOUR BY APPOINTMENT ONLY!!
NO WALK-INS
